
We don’t even debate why mobile apps are essential parts of everyday life. As mobile phone users, we can’t imagine our lives without apps. Consequently, the user base of mobile apps is only growing day by day. The extent can be gauged from these statistics from Statista:
The Statista Digital Market Outlook estimates that revenue across most segments will increase over the next few years and overall will reach around 613 billion U.S. dollars by 2025.
This does project a very good scope for mobile app developers in the near future. As the demand is high, they can expect a good market.
The demand for apps continues to grow for all types of devices and operating systems. Consequently, both Android app developers and iOS app developers are in heavy demand. But the number of players in the market is also increasing, giving tough competition to each other. So, what will decide which player wins the race?
Security as Game Changer
The answer is simple! With the growing usage of mobile apps, and a high level of technology upgrades, the vulnerability of apps is also increasing. So, the developers who can make highly secured apps will beat the competition and emerge as market players.
Top Mobile App Development Security Practices
We can straight read further to know how to keep apps secured. However, it is essential to understand that security practices also change with time and changing requirements and trends. So, while some measures are followed for years, some more should be specifically included for your unique needs.
It is not possible to list all the security measures for mobile app development and so we have tried our best to include the common, crucial, and trending security practices for your reference.
Security in Coding
The biggest aspect of mobile app development that can decide the success of the app is coding. So, we can say that even security has to be implemented well through coding else you can’t expect to build a secure app.
Security measures in coding depend on the tools, technology, and even the language that you are using to code your app. Many frameworks, tools, and languages come with inbuilt security provisions which can be very simply inherited into your code. For specific needs, you will have to build specialized code fragments. These needs vary with the type of app, the industry it is catering to, and even the type of users it targets.
We can’t discuss all possible security practices that can be implemented during coding as we have already discussed how these are need specific. However, some practices are common to almost all types of apps and so we must be aware of these. These commonly used security practices in coding are input validation, authentication, and authorization, avoiding buffer overflows, preventing SQL injection attacks, using safe cryptography algorithms, etc.
It's fine if you aren't technical and don’t understand all of these security practices of coding. It is more important to hire the best mobile app developers who will include all these security measures while developing your app.
Suggested Reading: How to Find Your Perfect App Development Team
Communication Security
So much communication happens through the app. User-to-app communication should be secure so that the user’s data and interactions are safe and secure. However, a bigger threat is the vulnerability in app-to-server communication. It can be a serious threat to sensitive user data and can go unnoticed for a long period.
Here are some measures for keeping app communication secure.
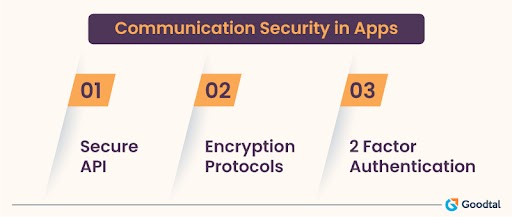
Let’s discuss each of these in brief!
Secure API
The first and foremost security practice for developers is to use secure APIs for the development of the app. This is non-negotiable and so always go for experienced developers who can identify the best APIs and avoid vulnerable ones. The choice of API differs with your requirements and so, expert developers who have worked with different APIs and varied types of apps can best identify the right API for your project.
Using Encryption Protocols
It is now a common practice to use Transport Layer Security (TLS) or Secure Sockets Layer (SSL) protocols to encrypt communication between apps and servers. This prevents malicious access to data.
Two Factor Authentication (2FA)
Two Factor Authentication is not new for app developers. It is implemented as an additional layer of security. It requires the user to provide two identification stages to gain access to the app. For example, the user can be asked to give both password and fingerprint.
Minimal Access & Privileges
User requirement analysis must cover essentials such as what data and resources must the app access and what should be restricted. If the app is developed keeping in mind that access should be given only to the minimum data and resources, the app is liable to keep data and resources secure.
This is not all! Users also pose a security challenge to the app and so businesses should go with the least privilege principle to ensure security. Users should be granted minimal possible access based on their roles with the app. Modern mobile app development is capable of incorporating comprehensive privilege hierarchies and so this is not a challenge that can’t be helped.
Regular Updates
We must know why we need regular app updates. If we have already made a great app, won’t that suffice for its success? And, why do we need technology upgrades? It's because hackers are targeting apps and finding new hacks to breach them. In no time, they can identify loopholes and find ways to crack your app.
Despite including all the security measures in coding you can’t ensure a secured app unless you are keeping track of the changing technology and needs. With changes in trends and technology, your app becomes outdated and vulnerable to security threats. So, you must continually upgrade your app to newer versions as and when required.
Moreover, it is imperative to keep all software components up to date including the libraries and frameworks. This ensures that the latest security patches are included and your app is secured against all threats.
Apart from the above, mobile apps must also be updated to fight against prevalent bugs or security threats. This is challenging, particularly because the bug has to be identified and countered without wasting any time.
Secured Push Notifications
We all know about push notifications. But, how many of us understand that push notifications can be a security challenge and so must be secured?
Well, the logic is simple! Push notifications are vulnerable to interception and tampering. Encryption in push notifications helps prevent interception or unauthorized tampering. It helps keep notification content secure and private.
Push notifications are also a great way to alert the user or notify them about security patches and updates. So, when you have released a security upgrade, users can take the necessary steps as guided and prevent security breaches in the app.
So, overall, push notifications are necessary for implementing security, while still vulnerable to security breaches. Thus, we must find ways to keep push notifications secured for greater app security.
Testing
Testing has been there since almost the same time as mobile app development. We all know that app testing is now a norm at all levels of development and not just pre-launch. Thus, mobile app testing has evolved into a separate field with professionals specifically skilled at designing and executing relevant test cases for every stage.
Performing regular security testing of the code helps identify and correct security vulnerabilities. Such checks and corrections also ensure that you do not encounter bigger security challenges at later stages. Moreover, testing and modification at earlier stages is less time and resources exhaustive compared to developing an app from scratch after the app fails post-development.
Testing is an art that even requires challenging one's own beliefs and perceiving the user’s needs and perspectives. Even the best developers might fail in testing. Moreover, developers can't dedicate their time and energy to such a comprehensive process at all stages of development. So, hiring the best mobile testing services can save you loads of time and effort, and guarantee success.
Finally! What Did You Achieve?
A secured application!

Wrapping Up!
Android app development companies and iOS app developers are trying their best to leverage the growing market demand for mobile apps. Agility is the key to staying ahead in the competition.
While the others are relying on outdated practices, the one who catches the trends, and implements the latest security practices will rule the mobile app development market. However, how simple is that? Well, it is not. It involves hard work and persistence. It will also involve learning new skills and upgrading the existing ones. All of these are time-consuming and costly.
A team of highly skilled professionals including the best developers, managers, security testing experts, etc., can ensure that your app is immune to all possible security threats. They will have to work even after the app development is over, detecting security threats, working to build patches, releasing regular updates, and keeping up to date with the latest technology to be able to do all of that. So, only go with the top Android app developers or iOS app development companies for the best results.
